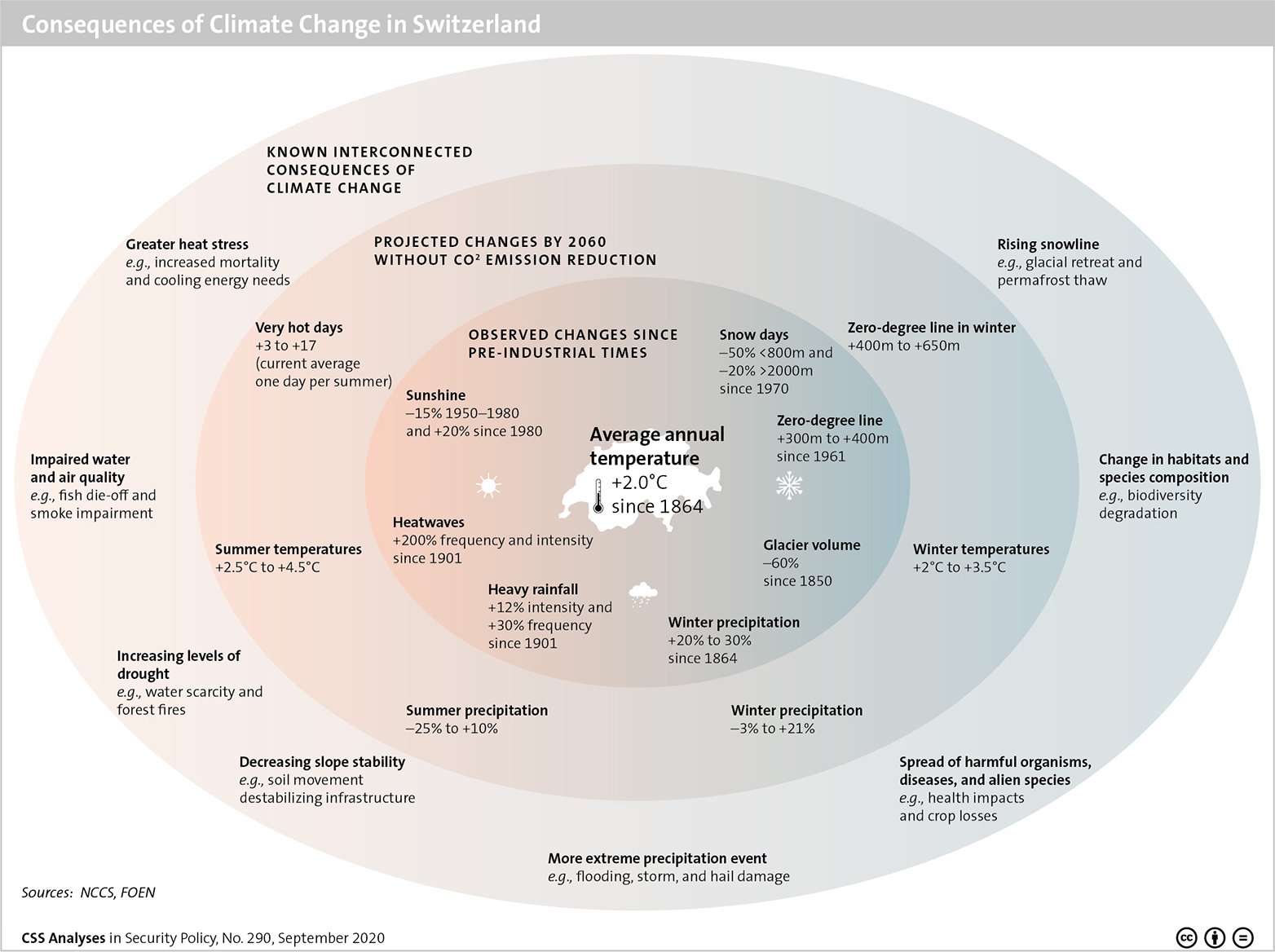
This week’s featured graphic illustrates the consequences of climate change in Switzerland. For more on Climate Change in the Swiss Alps, read Christine Eriksen and Andrin Hauri’s CSS Analysis in Security Policy here.
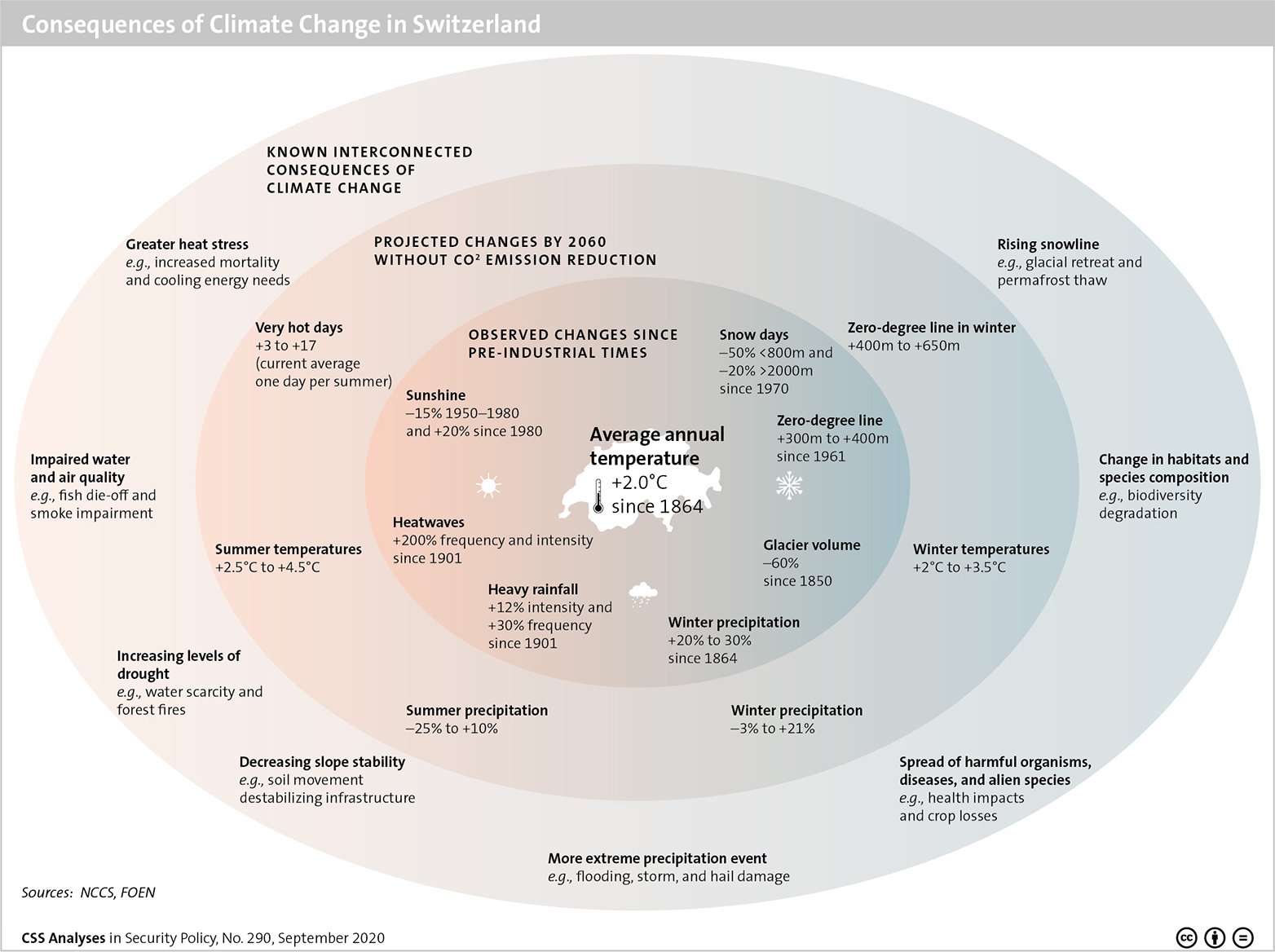
This week’s featured graphic illustrates the consequences of climate change in Switzerland. For more on Climate Change in the Swiss Alps, read Christine Eriksen and Andrin Hauri’s CSS Analysis in Security Policy here.

Im Ernstfall kann eine rechtzeitige öffentliche Warnung vor Extremereignissen Leben retten. Die Schweiz setzt dabei derzeit auf einen Mix aus Sirenen, Radio, Fernsehen und der Warnapp «Alertswiss». Da beinahe alle SchweizerInnen Mobiltelefone besitzen, könnte dieser Mix um Cell Broadcast ergänzt werden.
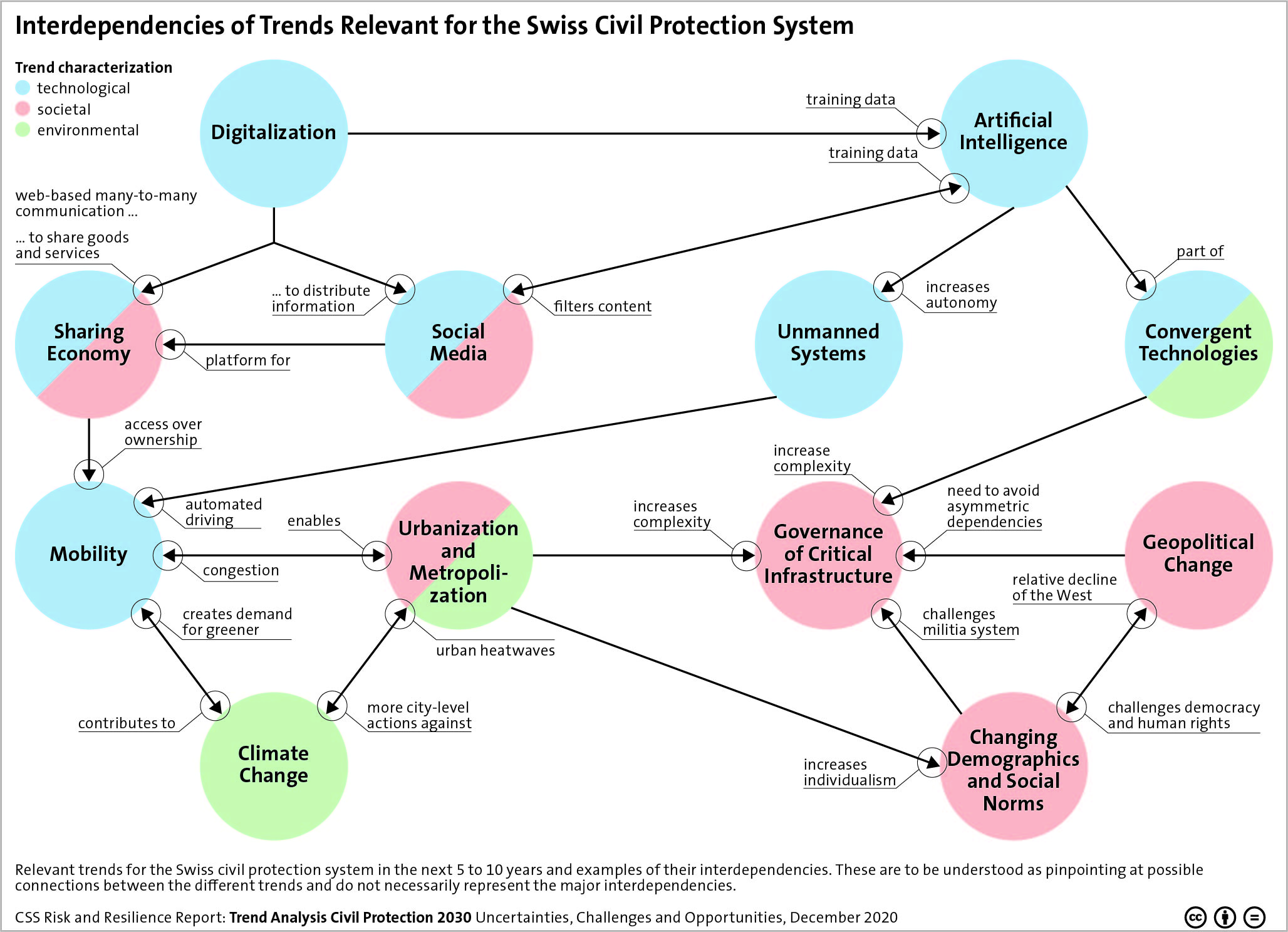
This week’s featured graphic points out the interdependencies of trends relevant for the Swiss Civil Protection System. For more on uncertainties, challenges and opportunities of trends in civil protection, read Andrin Hauri, Kevin Kohler, Florian Roth, Marco Käser, Tim Prior, and Benjamin Scharte’s CSS’ Risk and Resilience Report here.
During the repatriation operations in response to the COVID-19 pandemic in spring 2020, Switzerland benefited directly and indirectly from the activation of the European Union Civil Protection Mechanism (UCPM), despite not being a Participating State thereof. The increasing severity of natural and socio-technical hazards and their far-reaching consequences underscore the importance of international collaboration in other crises beyond the current pandemic. A new CSS Risk and Resilience Report, commissioned by the Swiss Federal Office for Civil Protection (FOCP), therefore assesses the costs and benefits of potential Swiss participation in the UCPM.
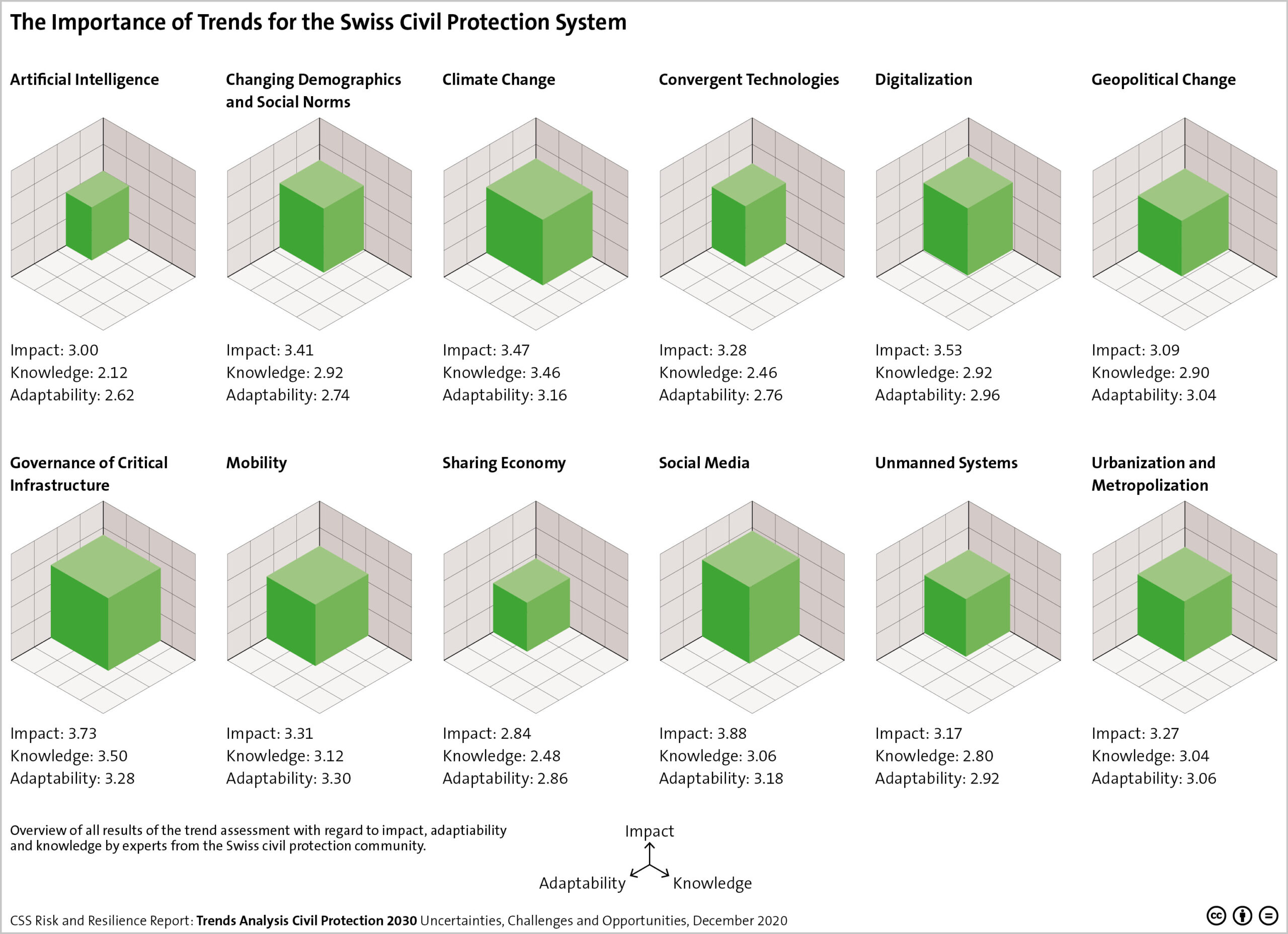
This week’s featured graphic points out the importance of trends for the Swiss civil protection system. For more on uncertainties, challenges and opportunities of trends in civil protection, read Andrin Hauri, Kevin Kohler, Florian Roth, Marco Käser, Tim Prior, and Benjamin Scharte’s CSS Risk and Resilience Report here.