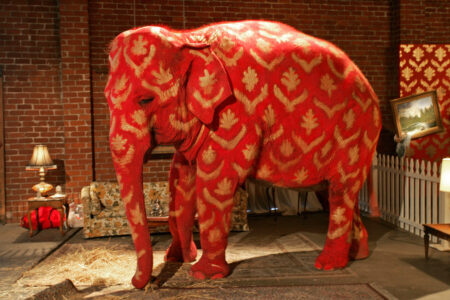
Image courtesy of Alamy.
Mediation Perspectives is a regular series of blog contributions by the CSS Mediation Support Team and occasional guest authors.
Culture becomes the elephant in the room when people do not acknowledge how implicit values shape conflict. “Truth” appears in multiple forms depending on which lenses we are using to view the world. This blog is based on a publication called “Inviting the Elephant into the Room: Culturally Oriented Mediation and Peace Practice”, reflecting insights from the work of UK mediator, Dr Zaza Elsheikh, who places culture and religion at the center of her practice. The blog explores a case from Zaza’s experience and ends with three insights from Zaza’s community mediation, which I believe have useful applications for the peace mediation field, namely regarding power, entry points and mediation success.