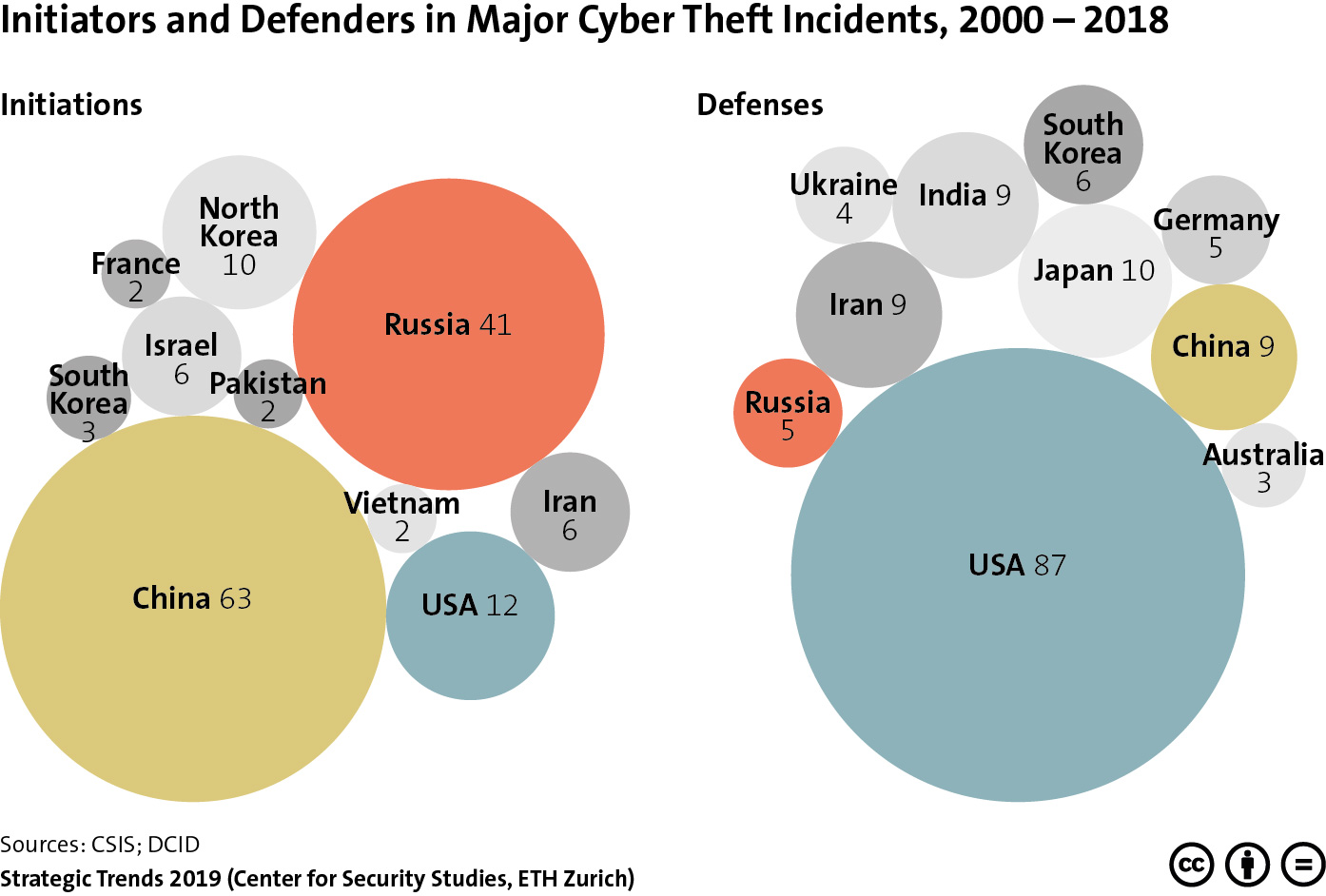
 This graphic provides an overview of the nations in which major cyber theft incidents were initiated, as well as the countries affected by these attacks between 2000 and 2018. To find out what this highlights about the eclipse of Western military-technological superiority, read Michael Haas’ chapter for Strategic Trends 2019 here. Strategic Trends 2020 is out on 30 April.
This graphic provides an overview of the nations in which major cyber theft incidents were initiated, as well as the countries affected by these attacks between 2000 and 2018. To find out what this highlights about the eclipse of Western military-technological superiority, read Michael Haas’ chapter for Strategic Trends 2019 here. Strategic Trends 2020 is out on 30 April.
Tag: Cybersecurity
This article was originally published by the Real Elcano Institute on 17 March 2020.
Theme
With cyber operations serving as an instrument of foreign policy, it is fair to posit that cognitive factors that account for behavior in the physical domain are equally applicable to cyberspace.

This article was originally published by the Elcano Royal Institute on 27 February 2020.
Theme
While national cyber security strategies have proliferated worldwide in the past decade, most have been overwhelmingly focused on resilience at the expense of political values. This paper addresses the challenges that have arisen from an overly technical focus on cyber security that has failed to consider the application of value sets in strategy creation.

This article was originally published by the Council on Foreign Relations on 18 February 2020.
Born in the 1990s, the thinking on cyber deterrence was nurtured by the U.S. Department of Defense in numerous war-gaming exercises. Hitting puberty in the aftermath of the distributed denial-of-service campaign against Estonia in 2007, cyber deterrence matured after Stuxnet and received peak attention from policymakers and academics from 2013 to 2016 during the golden age of ‘cyberwar’ scholarship. From 2016 onward, the interest in cyber deterrence started to fade to the extent that it is now intentionally neglected. The figure below captures this short life cycle by quantitatively visualizing the number of articles, book chapters, and research reports written on ‘cyber deterrence’ and ‘cyberdeterrence’ between January 1990 and January 2020.
This article was originally published by the Council on Foreign Relations (CFR) on 3 February 2020.
Many universities are starting to include cybersecurity as a course of study. While there is a high degree of variation between the selected readings of the syllabi of cybersecurity courses across different universities, there is some thematic overlap. By reviewing the syllabi of university cybersecurity courses, the authors seek to systematically evaluate this nascent field and advance its maturity.
