
This article was originally published by the Council on Foreign Relations on 18 February 2020.
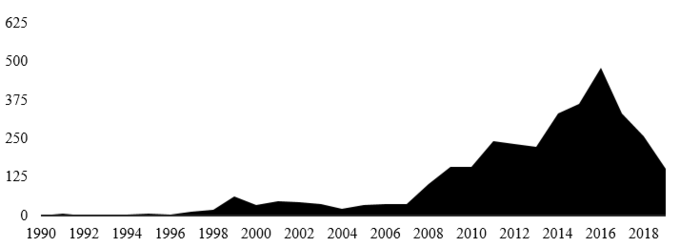
Born in the 1990s, the thinking on cyber deterrence was nurtured by the U.S. Department of Defense in numerous war-gaming exercises. Hitting puberty in the aftermath of the distributed denial-of-service campaign against Estonia in 2007, cyber deterrence matured after Stuxnet and received peak attention from policymakers and academics from 2013 to 2016 during the golden age of ‘cyberwar’ scholarship. From 2016 onward, the interest in cyber deterrence started to fade to the extent that it is now intentionally neglected. The figure below captures this short life cycle by quantitatively visualizing the number of articles, book chapters, and research reports written on ‘cyber deterrence’ and ‘cyberdeterrence’ between January 1990 and January 2020.
Why has the concept fallen out of fashion? The existing literature has certainly done a great job of providing a comprehensive list of reasons why deterrence in cyberspace is more difficult to achieve than deterrence in conventional domains. Cyberattacks are said to be cheaper to execute, while defense is hard. Retaliation in cyberspace is supposedly harder to execute as the attribution of a cyberattack necessitates time-intensive, all-source information, often spanning numerous networks and actors. Signaling is equally problematic, given the secrecy of cyber operations and the difficulty of discerning between offensive and defensive behavior. Furthermore, given the diversity of actors in this domain, including individuals, non-state hacking groups, and military operators, the assumption that all actors in cyberspace act rational is not a given.
Citing these problems has led to an equally comprehensive set of proposals that have provided variations of the deterrence logic. Joseph Nye Jr., for example, suggests that policymakers could focus on deterrence by economic entanglement and norms to overcome barriers to cyber deterrence. Uri Tor proposes the notion of cumulative cyber deterrence, which argues that defenders should not seek to deter individual attacks but a series of attacks. Similarly, Lucas Kello argues under the notion of ‘punctuated deterrence’ for a series of actions that generate cumulative effect, rather than tit for tat responses. Aaron Brantly borrows from the criminology literature to explain why limited forms of cyber deterrence might be possible.
However, comprehensiveness alone would not explain the decline as other fields of deterrence research remain equally prolific. The nuclear deterrence literature, for example, is still going strong.
An alternative explanation might be that the concept of cyber deterrence has been strongly tied to particular perception of the cyber threat: how to prevent an attack against the “physical layer” of cyberspace. Indeed, in the opening of their 2010 book, Richard Clarke and Robert Knake discuss a takedown of a U.S. power grid they liken to a “cyber pearl-harbor”. The final chapter concludes with a discussion of the pillars of cyber deterrence. Yet, since the 2016 U.S. presidential election, attention has increasingly shifted to cyber-enabled information warfare and influence operations as the major threat to national security. With the focus now less on the physical layer and more on the information layer of cyberspace, cyber deterrence has fallen out of fashion.
Examining the future debate on cyber deterrence, we see it splitting in two directions. The first will seek to explore strategic concepts that stand apart from traditional deterrence thinking. The U.S. Cyber Command strategy of persistent engagement is one idea that takes this direction. The goal of persistent engagement is not deterrence but limiting an opponent’s opportunity to act. Early contours of this re-thinking were already found in a 2016 article by Richard Harknett and Emily Goldman, talking about cyberspace as an environment in which “the contest between offense and defense is continual [and] the defense is in constant contact with the enemy.” Harknett and Michael Fischerkeller further refined the idea a year later, arguing that “[i]n an environment of constant contact, a strategy grounded in persistent engagement is more appropriate than one of operational restraint and reaction [i.e., deterrence] for shaping the parameters of acceptable behavior and sustaining and advancing U.S. national interests.” A similar point was made by Michael Sulmeyer, now at U.S. Cyber Command, which argued that the United States should focus less on deterring and spend “more time preempting them [cyberattacks] and degrading their ability to [hack]. It is time to target capabilities, not calculations.” Equally, older concepts such as active defense—defined as the “employment of limited offensive action and counterattacks to deny a contested area or position to the enemy”—might be re-thought and modified if the United States desires to increasingly operate outside of its own networks. While these ideas have already been challenged and refined, we can expect future writing on this topic to become even more prolific.
We are also likely to witness the emergence of new strategic concepts. Analysts from member states of the European Union can be expected to promote ideas that stand in stark contrast to U.S. thinking. While most EU member states have absorbed early U.S. thinking of cyberspace being a warfare domain and the need for cyber deterrence, European policymakers are uncomfortable with adopting much less discussing persistent engagement, as it is perceived as overly aggressive. Similarly, most European military cyber organizations will not be able to increase their operational capacities to such a degree that they can navigate “seamlessly, globally, and continuously,” as persistent engagement demands. Recognizing these limitations, EU member states will have to fill this strategic vacuum with creative conceptual thinking.
The second direction of research will seek to revitalize the thinking about cyber deterrence by placing it more centrally within conventional international security and deterrence paradigms. Aaron Brantly, for example, argued back in 2018 that the main challenge of the future is not to define deterrence in cyberspace, but to “understand the role digital technologies play in the broader scope of interstate deterrence.” In the same year, Andrew Futter published a book explaining how the nuclear order can be influenced by the cyber threat. A recently published edited volume of Jon Lindsay and Erik Gartzke on cross-domain deterrence, with a chapter on cyber deterrence, equally moved in this direction. As the scholars write, “cross-domain deterrence is not new today, but its relevance is increasing. Strategic actors have long combined capabilities or shifted domains to make coercive threats or design around them […] As a larger and more diverse portfolio of tools available for coercion complicates strategic choices, a better understanding of [cross-domain deterrence] becomes a critical asset for effective national security strategizing.” An important question for this future research, however, will be, to what degree this growing portfolio of “available means,” and the development of cyber tools in particular, will be more or less stabilizing.
While the significant drop-off in publications on cyber deterrence in 2016 suggests an intellectual maturation, these two research directions are likely to re-energize the topic. Long live cyber deterrence!
This article is published under a Creative Commons Attribution-NonCommercial-NoDerivatives 4.0 International licence. (CC BY-NC-ND 4.0)
About the Authors
Max Smeets is a senior researcher at the Center for Security Studies (CSS) at ETH Zurich and affiliate at Stanford University CISAC.
Stefan Soesanto is a senior researcher in the Cyber Defense Team at the Center for Security Studies (CSS) at ETH Zurich.
For more information on issues and events that shape our world, please visit the CSS website.

