This article was originally published by War on the Rocks on 11 September, 2015.
After the OPM hack, there were suggestions that the Chinese might be building digital dossiers on every U.S. government official, or even on all Americans. More recent reports have the Russian and Chinese intelligence services exploiting personally identifiable information about Americans from security clearance databases, airline records, medical records and many other sources on a massive scale. The Los Angeles Times has reported that the head of the National Counterintelligence Executive has confirmed that foreign powers are doing these things. Other, anonymous sources told the Times that “at least one clandestine network of American engineers and scientists who provide technical assistance to U.S. undercover operatives … overseas has been compromised as a result.” It has even been suggested that the Russian and Chinese services are throwing data from the Ashley Madison breach into the mix.
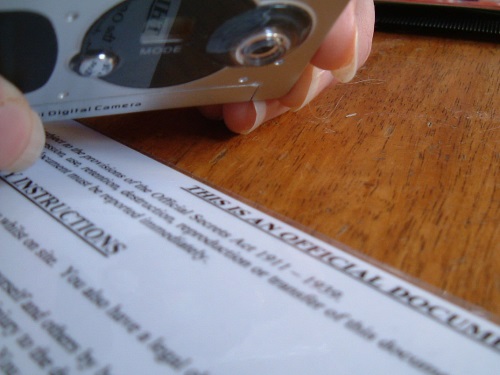
This is not the first time that the U.S. government has feared that the nation’s adversaries were building large numbers of dossiers on its officials. Documents held in the National Archives give us a tantalizing glimpse of a similar round of concern a century ago. Back then, however, the cutting edge information technology was the card file, not the computer.
War Department records contain the March 1917 correspondence between Leland Harrison, the State Department’s intelligence coordinator, and Maj. Ralph H. Van Deman, the War Department’s intelligence chief, an officer whose greatest interest was counterespionage. On March 10, 1917, Harrison wrote to Van Deman asking him to validate information about an Army officer named Frederick Stetson that purportedly had been “taken from a card” held by the Germans. (There was no indication of how Harrison came into possession of this information from Germany.) Harrison added, “I have reasons to believe that similar cards regarding every officer of the United States Army are in the possession of the German Government.” A few days later, Van Deman responded, apparently confirming the information about Stetson. (Sadly, the file at the National Archives contains only cover memos, not the attachments that contained the substantive information.) Van Deman was even more worried than Harrison, however, writing, “I think you are entirely correct in believing that the German Government possesses records of every officer in our service, not only those in the Army, but those in the Navy also, and I feel very sure that the same system is carried out with respect to officers of other countries.” A few days later, Van Deman responded to another similar query from Harrison. The subject this time was Dennis Nolan, who in a matter of weeks would be named the G-2 for the American Expeditionary Forces heading to France.
Yesterday’s concerns about foreign card files and today’s concerns about foreign digital dossiers have in common a perception of a highly capable enemy. But there is also a difference. A hundred years ago the idea of an enormous and ruthlessly effective German intelligence service operating with … well … German efficiency, was taken as an article of faith, but now we know that it wasn’t true. Today, however, it is a fact that Chinese entities steal data from the United States on a remarkable scale and that the Russians are not far behind them. We also know that modern computing makes the effective exploitation of big data entirely possible. In short, if Beijing and Moscow aren’t putting together digital dossiers on millions of Americans, they are missing an invaluable opportunity. The Kaiser would be jealous.
Mark Stout is a Senior Editor at War on the Rocks. He is the Director of the MA Program in Global Security Studies and the Graduate Certificate Program in Intelligence at Johns Hopkins University’s School of Arts and Sciences in Washington, D.C.
For more information on issues and events that shape our world, please visit ISN Security Watch or browse our resources.

