
This week’s featured graphic maps the states of the Western Balkans. To find out about the rearmament in the Western Balkans, read Andrej Marković and Jeronim Perović’s CSS Analysis in Security Policy here.

This week’s featured graphic maps the states of the Western Balkans. To find out about the rearmament in the Western Balkans, read Andrej Marković and Jeronim Perović’s CSS Analysis in Security Policy here.
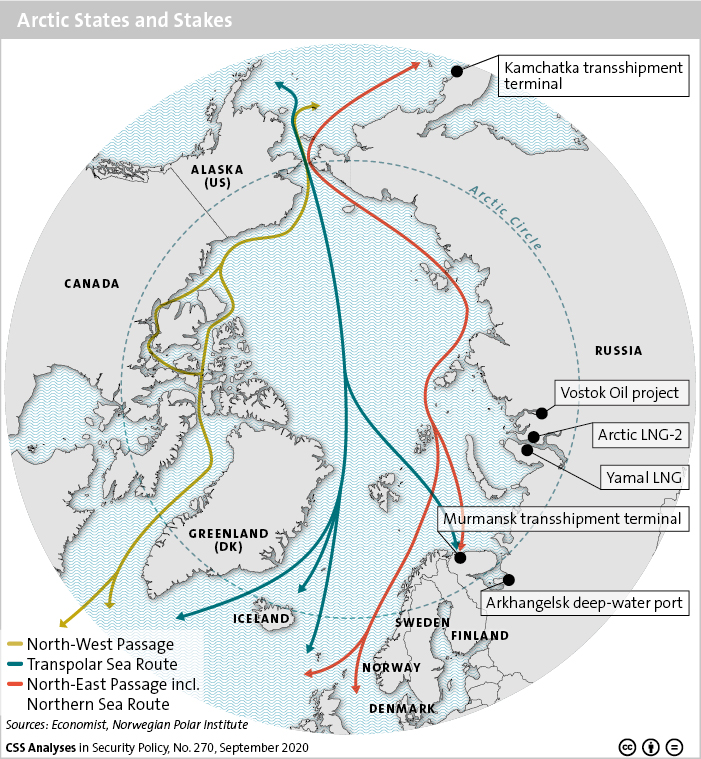
This graphic maps the countries located in the Arctic Circle, as well as its passages and sea routes. In the Arctic, Russia and China have their own ambitions, but their objectives currently overlap. Complementary economic interests are the main driver of their cooperation.
For more on the Sino-Russian dynamics in the Arctic, read Maria Shagina and Benno Zogg’s CSS Analysis in Security Policy here.
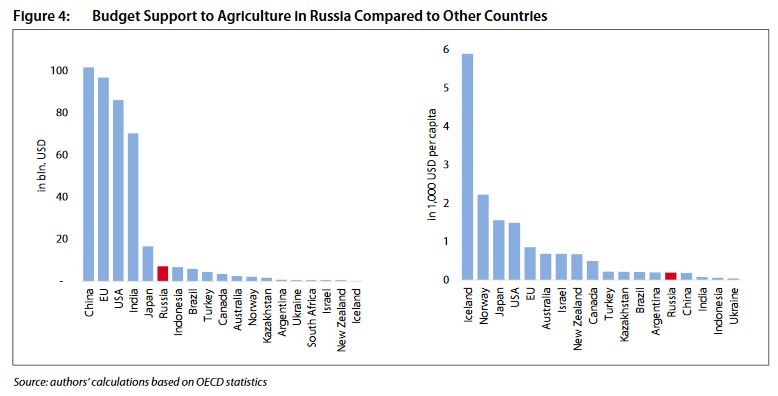 While support for innovations and the provision of digital technologies for agriculture are declared as being among the Russian government’s policy priorities, those activities are not prioritized in budgeting. This graphic compares the budget support to agriculture in Russia with that of other countries.
While support for innovations and the provision of digital technologies for agriculture are declared as being among the Russian government’s policy priorities, those activities are not prioritized in budgeting. This graphic compares the budget support to agriculture in Russia with that of other countries.
For more on the structure of agricultural production, trade development and agri-food policy in Russia, read this issue of the Russian Analytical Digest.
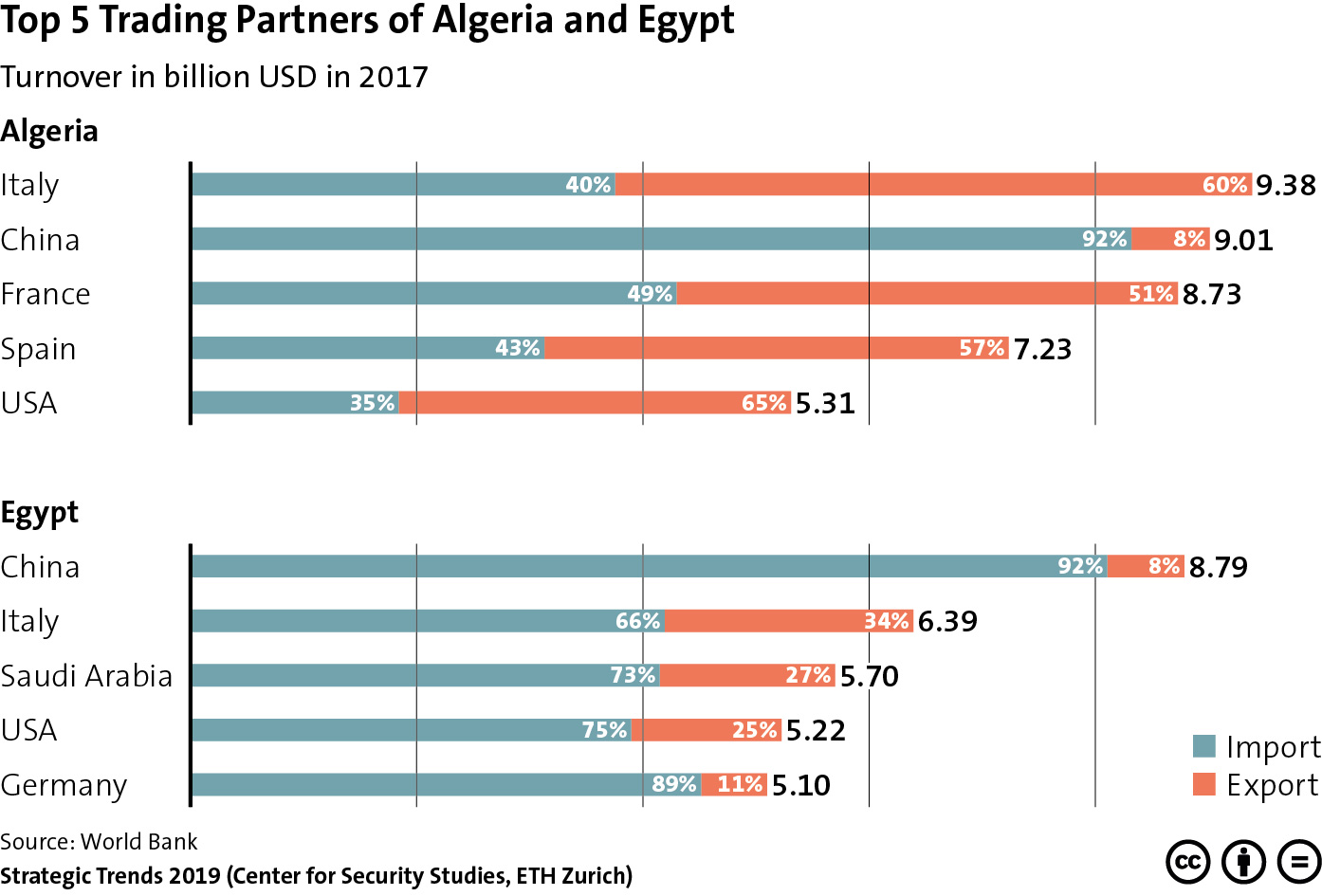
This week’s featured graphic provides an overview of Algeria and Egypt’s top trading partners. Russia’s absence from the top five trading partners list of either country highlights that despite Moscow’s revival of its ties with Cairo and Algiers, it remains overshadowed by other actors in the economic sphere.
To find out more about Russia’s strategy in the Middle East and North Africa, read Lisa Watanabe’s chapter for Strategic Trends 2019 here.

Image courtesy of U.S. Embassy Kyiv Ukraine/Flickr.
Russian foreign policy needs to be understood and adequately addressed for diplomacy to have a chance for a comeback in NATO-Russia relations. Here, the election of Joe Biden as US president could serve to reverse the worrisome tendencies in US foreign policy under Trump and restore pragmatic dialog and direct military contacts with Moscow. Calls from expert communities for rebuilding the arms control architecture to reduce the risk of unintended incidents and escalation are growing louder.